Red Balloon Security, Atredis Partners Announce Strategic Partnership
January 02, 2020
News

The purpose of the partnership is to protect corporations, manufacturers and suppliers against hard to detect firmware-based threats.
Red Balloon Security and Atredis Partners, embedded device security companies, announced a strategic partnership, in a press release. The purpose of the partnership is to protect corporations, manufacturers and suppliers against hard to detect firmware-based threats.
"We look forward to working with Atredis to deliver robust security solutions for embedded device manufacturers, developers and users," said CEO of Red Balloon Security Dr. Ang Cui.
The collaboration will leverage both firms' expertise and capabilities in critical areas of embedded device security. Red Balloon is a developer of firmware-based security, while Atredis provides advanced security testing, firmware analysis and assessment services.
Red Balloon Security's flagship product, Symbiote Defense, is the first universal embedded defense for all embedded devices and was originally developed in Columbia University's Intrusion Detection Systems Lab, per the release.
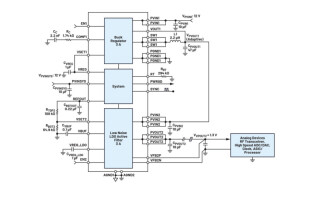
It is a platform-independent, OS-agnostic, real-time, host-based intrusion defense that is injected into the firmware of the device. It defends devices without requiring any code change from the vendor, any additional or upgraded hardware, and all without impacting the functionality of the device. Symbiote Defense is designed to protect any and all embedded devices, from printers to PLCs. It can be applied to any device regardless of OS, CPU type, or hardware. The technology detects any unauthorized attempts to modify the firmware's code or data within a fraction of a second, regardless of whether the device is in sleep mode, or busy servicing requests.
Atredis takes a research-centric approach when evaluating complex hardware, firmware and embedded operating system targets. Atredis works closely with a company's leadership, engineers and developers to achieve a sound understanding of the design, architecture and threat scenarios to model out in its assessments.
For more information about Red Balloon Security and Atredis Partners, visit www.redballoonsecurity.com and www.atredis.com.