Employee-Specific Hardware-Based Licensing Defeats Internal Security Threats
November 09, 2021
Blog

Just as you want to secure your application against outside threats, preventing internal threats is also essential to software security. Numerous internal actors can access source code, alter development processes, and distribute company-specific trade secrets. By implementing employee-specific hardware-based licensing, you can strengthen security, boost revenue, and slash your employees’ need for support.
What is Employee-Specific Hardware-Based Licensing?
This licensing method is simply a way to give certain employees access to your software depending on various traits. You can choose from a wide range of options to establish the two components of employee-specific hardware-based licensing:
- Employee-specific: You need a way to divide your employees into groups that will be granted different levels of access, such as by their roles or qualifications.
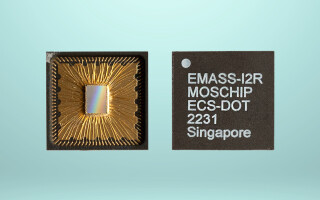
- Hardware-based: You need hardware, which means using dongles and/or hardware keys to control access to your application.
The hardware-based aspect of this licensing method is mostly self-explanatory, but we’ll discuss the employee-specific component in detail.
Employee Segmenting
You can give employees specific access to your company’s software applications based on many different factors. Fifty-five percent of organizations say their greatest security risk comes from employees who are given access to things they shouldn't have, so it's worthwhile to consider limiting access when possible. Here are a few examples of ways to categorize your employees:
- Employee tenure: You can enable application access based on an employee’s tenure at the company. This way, you grant access to established employees but restrict access for new employees. This restriction protects your company from vulnerabilities created by the negligent actions or inaction of an employee who doesn’t last.
- Employee certification tier: Limit access to your internal applications to employees who are licensed or certified to work with them. This measure ensures that a Level 1 employee is not creating or altering source code or accessing features they are not authorized to.
- Employee job title: Giving employees access based on their position is similar to basing it on tenure. It gives the higher-ups latitude to resolve any issues without requiring additional support.
- Employee job function: Another option is to give employees clearance to use certain features of your internal application based on their functional role or department. This method prevents employees from creating issues or vulnerabilities that affect other departments or job functions.
Why Do I Need Employee-Specific Hardware-Based Licensing?
Insider security threats are significant; in 2021, as many as 66% of organizations fear them more than external threats. Some of these potential hazards are due to employee ignorance or carelessness. Some come from employees who seek to benefit at the company’s expense, while others are the result of simple errors that anyone could make. Those caused by ignorance or carelessness can often be mitigated by training, but the ones that are due to maliciousness or human error typically require other measures, like more secure licensing methods.
Here are four examples of internal threats that can jeopardize your application’s security:
- Social engineering: Employees reveal confidential information to peers and get insight on company-specific trade secrets, then use them to their own benefit. In some cases, employees are tricked into revealing the information by someone outside the company.
- Illicit data sharing: Employees might share proprietary information online or by email. This is typically a careless mistake, like hitting the wrong button when sending an email.
- Poor regulation of devices: There are many ways to mishandle devices. For example, an employee might take work home on a device that is not secure. If the device gets hacked, the result can be an information leak. Another possible result of taking devices home is that they can be stolen. Both of these dangers can be present even if the employee is doing nothing wrong, such as if they decide to work in a coffee shop with an unsecure network or they leave their laptop in a locker at the gym.
- Use of third-party systems and services: When employees feel, consciously or subconsciously, that the tools they’ve been given to accomplish their work are not cutting it, or when they prefer another tool, they may turn to unauthorized third-party software, applications, or internet services. The problem is that IT departments can’t regulate the use of these tools, which has earned them the name shadow IT. Beyond compromising your company’s ability to regulate them, these tools may have inferior security.
How Can Employee-Specific Hardware-Based Licensing Benefit Me?
Hardware-based security requires hackers to gain access to the physical dongle, so it eliminates their ability to pirate your software remotely. It also doesn’t require an internet connection, which means it keeps safeguarding your application when internet use is restricted or unavailable. Further, the security algorithms and even the application code can be run on a dongle instead of on the computer, adding another layer of security between your intellectual property and any internal threat that could compromise it.
Encryption is a further step in a solid hardware-based software licensing system. It can hide the communication between the dongle and the application, making it undetectable by hackers.
The conventional and inefficient approach is to approve access for those who request it on a case-by-case basis. Instead, you can decide ahead of time who needs access and authorize it before they need it. The result is greater efficiency: Employees can do their jobs without waiting around for permission, and your support department is no longer tied up with needless requests for access, so they can spend their time and effort addressing real needs in other areas.
Since it empowers your employees to work more efficiently and empowers you to prevent mistakes that result in reparative spending, employee-specific hardware-based licensing can cut costs, which translates to more profit.
A Targeted Licensing Solution
Software licensing that blocks outside threats is vital, but you need just as much protection against threats that can endanger your application’s security from the inside. Although these risks may not come from malicious actors, they could result in just as much damage.
Employee-specific hardware-based licensing constructs a virtual wall around each employee to shield your company from vulnerabilities, including threats from unwitting employees who are just trying to do their jobs well. This specific approach to software licensing increases security to unprecedented levels, which keeps your company running efficiently to maximize profits.