Securing Smart Cities Against Cyberattacks
September 01, 2021
Story

We’re reliably told that the future of urban living is smart cities, in which mass-scale data gathering provides insights and real-time management that enable large populations to live together in a more comfortable and sustainable way than they do now. The question is, will smart cities be reliable?
It’s worth thinking ahead about this issue a little, given recent events. The snowstorms in Texas in February 2021 reminded us that we can’t just assume that the infrastructure that makes our cities possible will always be available and work properly, come what may.

Wills Point, Texas February 2021: You can’t always rely on physical infrastructure. (Photo by Matthew T Rader on Unsplash).
It’s actually real physical stuff that wears out, breaks down, or is overwhelmed by events. And when it fails, it fails in ways that rapidly propagates disruption to other areas. The second recent event worth considering when assessing the future of smart cities is the SolarWinds hack of the US government. A poisoned update of IT company SolarWinds’ widely used monitoring tools was used to enable hackers to penetrate multiple departments of the US government. Again, a single point of failure at SolarWinds rapidly propagated enormous amounts of disruption to many other organizations. Smart cities will need powerful security features if they are to avoid both forms of vulnerability.
Nonetheless, the global pandemic has prompted many people to reassess how and where they live and work, and for those who want to remain in cities, what they expect of them. Perhaps urban spaces in the future will be designed to offer a high quality of life, rather than being geared towards office work and economic activity – with more green spaces and communal working, and fewer offices and sandwich shops.
This vision may be made possible by smart cities, urban areas in which electronic data is gathered and analyzed to help make decisions about the best ways to manage aspects of urban living. This approach relies on the widespread deployment of Internet of Things (IoT) devices and the analysis of the resulting data using techniques ranging from traditional statistical analysis through to machine learning and other artificial-intelligence strategies.
The goal of a smart city is twofold. The first is to add control and monitoring systems to physical infrastructure, such as sewage, water, street lighting, apartment blocks, and traffic control, to make the city more sustainable and efficient. The second is to give urban dwellers more involvement in how their cities operate, by giving them the power to make collective decisions about them.
The easiest way to create a smart city is to add an IoT ecosystem overlay to an existing built-up area. This is already happening, according to research conducted by Smart Cities World together with Philips Lighting. It concludes that the three best smart cities in the world are Singapore, London, and Barcelona.
Making a city smart can start on a small scale, for example by installing traffic sensors to control traffic lights so that traffic flows more smoothly or adding sensors to a public transport network and making the resultant data feeds public so anyone can use them.
The more challenging way to make a smart city is to build it from scratch. For example, Qatar is planning to build a smart city called Lusail on 38km2 of desert outside the capital Doha. Saudi Arabia is planning to build a smart city called NEOM by 2030. Egypt is planning to build a new capital city in the desert. Even Bill Gates, the Microsoft billionaire, got involved in a planned smart city named Belmont, to be built in the desert 45 miles west of Phoenix, Arizona.
According to a 2017 statement from the project’s backers: “Belmont will create a forward-thinking community with a communication and infrastructure spine that embraces cutting-edge technology, designed around high-speed digital networks, data centers, new manufacturing technologies and distribution models, autonomous vehicles and autonomous logistics hubs.”
And there’s the challenge of smart cities: the cyber infrastructure is so interwoven with the physical infrastructure that the whole city becomes vulnerable to cyberattacks. The complexity of such systems, and the way that it enables the propagation of breaches among their various subsystems, also makes it seem that getting hacked will be inevitable.

Cyber infrastructure is so interwoven with the physical infrastructure that the whole city becomes vulnerable to cyberattacks.
Hacks could include attacks on the control systems governing utilities, such as creating electrical blackouts or interfering with sewage treatment. Traditional cities are already facing ransomware attacks, and smart cities would be an even more attractive target because of their greater vulnerability.
If we’re going to go forward with smart cities, the enabling IoT ecosystems will have to include strong security measures from the start. This will present challenges when IoT devices such as simple sensors, with very limited processing and memory resources, are allowed on to the IoT network. As with SolarWinds and many other cyber-attacks, in a networked environment a single weak link can undermine the security of the whole enterprise.
One of the most important steps in securing a smart city, therefore, is to find a way to ensure end-to-end security between IoT devices and the servers that control them. This can be achieved with devices that have strong identities and use correctly configured, implemented, and managed cryptography. Setting up these schemes becomes a challenge when IoT ecosystems grow to include millions of devices – configuring each device individually becomes impractical.
Each device needs to be able to identify itself in a way that cannot be impersonated. If devices lack strong identities, hackers can add fake devices to IoT networks by impersonating valid devices – opening a smart city to a wide range of malicious activities. We’re used to this kind of threat in the virtual world, but the cyber-physical systems that bridge the virtual and real worlds in smart cities make the threat particularly concerning. There is a considerable difference between the ‘blue screen of death’ of a hacked PC and actual deaths caused by a hacked traffic-management system.
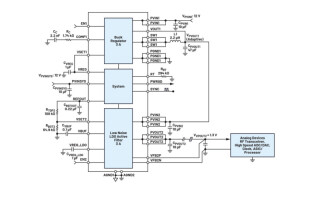
Each device therefore needs a strong cryptographic key that is shared between the device and the control hub. This can be achieved by using public-key strategies, which allow devices to receive secure communication from any entity that knows the public key. An IoT ecosystem would also need to be able to access public-key infrastructure, such as certificates signed by an authority, which would guarantee the authenticity of the public keys.
Public-key cryptography is widely used and well understood, but much more resource-intensive than symmetric key cryptography, in which communicating entities share a secret key and so need not go through the process of establishing a secure channel using public-key strategies. The problem with using symmetric keys is how to securely distribute them between IoT devices and central servers. The security challenge involved is considerable, given the many steps in the IoT supply chain from chip and device makers, through to distribution channels, firmware authors and IoT analysis tool vendors. But there are approaches, based on giving IoT chips unique and unclonable identities, which can mitigate the issue.
Smart cities, or some aspects of smart city technology, will play an important role in the next phase of urban living, especially if it can help increase both its sustainability and the quality of life for city dwellers.
When we build the infrastructure of smart cities, we should learn the lessons of history. A lot of the infrastructure of London, apparently already one of the world’s top three smart cities, was built in the nineteenth century. Decisions we make today about implementing smart cities need to be robust against today’s challenges, and able to deal with new forms of security risks that are as yet unforeseen. If we can achieve this, we will be able to build smart cities with confidence. If not, we may be trapped forever in dumb cities whose infrastructure was planned and implemented centuries ago.
Dr Charlie Grover is a cryptography researcher at Crypto Quantique, where he is driving performance improvements in securely extracting entropy, or randomness, from Physical Unclonable Functions (PUFs) in CMOS semiconductors. His work is contributing to further development of the world’s most secure root-of-trust technology for microcontrollers and application-specific integrated circuits (ASICs), where identities and cryptographic keys are developed inside these silicon devices on-demand, eliminating the need for key injection, key storage, or third-party involvement.
Charlie holds a PhD in Electrical and Electronic Engineering from Imperial College London, where he worked on lattice-based cryptography and other aspects of post-quantum cryptography. Before that, he was awarded a first-class Undergraduate and Master’s degree in Mathematics at the University of Oxford. His research interests are cryptography in a post-quantum world and hardware security IP for semiconductors.