Securing IoT Intellectual Property From Smart Manufacturing
July 19, 2021
Story

Securing the Internet of Things is a remarkably complex problem with several layers, and many manufacturers have shown they just don’t want to deal with it or don’t have the resources.
Fewer than 10% of consumer IoT companies follow vulnerability disclosure guidelines, let alone prioritize proper security at a foundational level.
The difficulties stem from how many security elements need to be considered. The devices or hardware must be secured first, as do the software solutions that empower them, whether that’s a proprietary onboard solution, a web-based application, or a mobile platform.
Then there’s the matter of intellectual property, or IP, and protecting trade secrets from the competition. It’s a crowded space, and these days, reverse-engineering products and various electronics is not challenging at all.
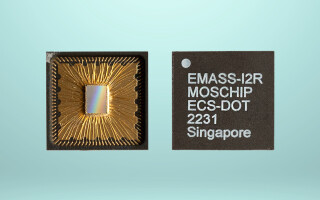
It calls for devices that are intelligently designed from the very start, with secure manufacturing processes and incredibly capable hardware and software deployments. For hardware, this means utilizing hardware security modules (HSMs) to manage cryptographic keys and digital certificates which provide a nuanced form of authentication. Breaking that down, it’s essentially encryption at the hardware level, where the digital certificates and keys are managed on the device, as opposed to remotely.
And for the software, IoT security and IP protection can be handled at the edge of the network. Why? Gartner predicts that 75% of all data generated will eventually be processed by edge computing solutions. It makes sense to start there when building up IoT software security.
It makes even more sense in manufacturing, where the incoming data isn’t necessarily going out to an open or internet-facing network.
Intellectual Property and the IoT
IP licensing agreements for computer software, websites, digital platforms, internet policies, and some advanced electronics — like IoT — have always been a strange beast. While protecting an IP is and always has been a fundamental part of doing business, the definitions and methods for doing so can be difficult to master.
There’s a lot to consider, especially when you’re talking about a system that includes proprietary hardware and software merged. That’s before even dealing with the monetization of intellectual property assets, whether directly or through a franchisor-franchisee relationship. Data is constantly flowing, too, and some of it is incredibly sensitive information. Securing all facets of the IoT and connected devices is monumentally complex. But that’s where smarter, more secure manufacturing comes into the picture.
Embedding security at a foundational level means thinking about it as early on as possible. During the conception and design stages, to start. Beyond that, it calls for ingenious manufacturing techniques like the aforementioned hardware security modules. Finally, it’s all about securing the flow of data, which is where the edge computing solutions are relevant.
Why Do IoT Security and IP Protection Matter in Smart Manufacturing?
An IoT device is designed to collect data and send that information to a home server through an active network connection. In this way, it empowers remote access, for the end user most importantly. There are many reasons why that active connection is necessary, including for authentication and security. It’s also important to point out that it can include both private and public networks, with or without internet access.
Imagine a smart door lock, for instance. A regular lock doesn’t care about who’s opening it, why, or when. It just knows that the physical key inserted is correct, or not. A digitally enabled lock, on the other hand, cares about whether it’s the right user, and whether they’re connecting with an authorized device, and it also collects performance data such as dates and times, what door or lock was activated in relation to other devices, and more.
All of this information is used to feed the system behind the scenes and then is ultimately passed on through mobile or web applications. IoT and smart manufacturing solutions work in exactly the same way.
Now, imagine if someone could reverse-engineer that lock to gain access to the home server. Imagine if they could create a comparable device that collects and snoops the transmitted data. What if they gain access to those systems remotely and seize control, alter the software, or worse?
The motives in this scenario don’t really matter. What’s important is that those things could all happen with an unsecured system and series of connected devices. That’s bad for everyone.
Now take that scenario and apply it to the industrial and manufacturing field. Hackers could seize control over mission-critical systems to alter devices and products, halt operations, and cause any number of severe complications. They could even alter the manufacturing of consumer devices to embed malicious code. Attackers are already targeting manufacturers frequently, so this scenario is not outside the realm of possibility.
Smart Manufacturing: Thinking About the Data
Protecting security foundationally requires thinking about that flow of data and information, and how it’s being handled. Where is it going and where is it being stored? What devices and systems have access? How do you ensure the data stream is protected?
That’s why hardware security modules are so useful. They force encryption at a hardware level, ensuring that whatever or whoever is accessing the system and data is an authorized party. What’s more, all data streams are encrypted at the source, which means without the proper cryptographic keys or certificates, they cannot be read, at least not without an extreme degree of difficulty.
Whether you’re talking about a smart home lock on a residence, a climate control system for a factory, or IoT sensors within manufacturing hardware, the secure encryption of data is vital to protecting the systems, users, and everything in between. However, it can require an inordinate amount of processing power to make all of these systems work.
Cue edge computing technologies, which are designed to handle computations and processing, and provide power closer to the edge of the network, rather than from the outside on a remote server or system.
By bringing the computations, processing power, and data storage closer to the source, or rather where it’s needed most, it speeds up performance and reliability. It also accelerates data-driven processes and applications, helping to realize the full potential of modern technologies. You’re not waiting minutes for a sensor or device to respond, but merely seconds.
All of this has major implications for the world of smart manufacturing and mission-critical production platforms.