Protecting the IoT with self-encrypting storage, part 2
July 28, 2016

As noted in part one of this blog, self-encrypting storage (SES) will increasingly be required to protect embedded products, especially as the Interne...
As noted in part one of this blog, self-encrypting storage (SES) will increasingly be required to protect embedded products, especially as the Internet of Things (IoT) expands. This encryption is already available in SED products. However, the next step is activating the drive and managing the authentication credentials to lock and unlock drives and only allow authorized access to the drive.
Unlike software-only encryption, an SED implements the cryptographic function in hardware, directly in the drive electronics. The cryptographic key(s) that govern the operations are generated on board the drive during manufacture and never leave the drive. Therefore, the keys are protected from external detection.
For embedded systems, the activating process depends on a few system-related aspects. Products with an operating system are the most straightforward. However, embedded applications that do not have an operating system can be more complicated. The Trusted Computing Group (TCG) specifications describe how this can be done, but for users who need a little help, TCG is a great resource to start putting the appropriate pieces together. Also, the Drive Trust Alliance (www.drivetrust.com) was created to promote SED/SES broadly by providing practical how-to advice and open-source SED client management software.
The layered approach
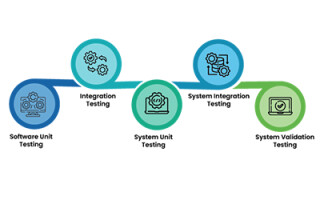
TCG has developed a layered approach to data security. It starts at the lowest layer with the storage device implementing TCG’s Opal 2.0 standard for SEDs and now Opalite (subset of Opal functions) and Pyrite (authentication and access control) security subsystems for SES in embedded systems. With this starting point, the specifications extend security to further levels for communications including Wi-Fi and more.
What can be done now?
Embedded application developers can expect to see TCG’s Opalite and Pyrite implemented in embedded memory in 2017. Then, further SES implementations into new storage environments will appear. The use of the various TCG specs will depend on the type of data stored in the device. A secure system could be designed to protect data structures used by the storage device.
At this point, it is important that developers of embedded systems are aware of both the storage security problem and the standards-based solution that has been developed to address it. As products become available from the vendor community, there will be more specific building blocks, including development kits, APIs and drives that come preprogrammed with the appropriate real-time OS commands and other development aspects.
Avoiding a false sense of security
It is important to understand that cryptography is not a panacea for everything. Embedded system designers need to analyze their products to determine and evaluate threats, vulnerabilities, mitigation and other aspects of security threats. For novices and those who have not performed a serious threat review, part of a good security solution is developing appropriate counter measures and mitigation plans.
Available threat analysis tools such as STRIDE, derived from an acronym for six threat categories developed by Microsoft or the seven steps of the Lockheed Martin Cyber Kill Chain enhance visibility into an attack and enrich an analyst’s understanding of an adversary’s tactics, techniques and procedures. NIST and the National Association for CPAs have guidelines for performing this analysis as well for executing very detailed audit/risk analysis.
Help to get started
SES is a major starting point for providing the foundation in the layered approach to embedded product security in the IoT. To start taking advantage of this security, TCG has several resources in all areas of security/trust, and specifically in storage protection, including specifications that explain how system designers should communicate from a host device to a storage device. Embedded storage suppliers can help system designers ensure that the stored data is secure. Other vendors that have embraced SES concepts can help with higher layers of data security, such as IBM, Microsoft, Absolute, Gemalto, and WinMagic. See TCG’s member list for details.